Information Security Policy Templates
Information Security Policy Templates - Using group policy objects (gpo) to add membership to a local group can create a security risk if the target group has excessive permissions or rights. Learn how to write an information security policy, and download two templates on cybersecurity and network security perimeter policies to get started. The following is a library of free information security policy templates that map to the hitrust common security framework, which in turn maps to a multitude of security frameworks (nist,. Sans has developed a set of information security policy templates. You can start with a data retention policy template that’s been approved by former auditors or bring your own existing policy into the platform. These policy templates align with cis controls v8 and v8.1, enabling. These templates are designed by industry experts who. Implementing a comprehensive information security management system (isms) compliant with iso/iec 27001:2023 standards. Regularly assessing the information security. Defines the protocols for using both personal and corporate devices to ensure sensitive information is protected. The templates can be used as an outline of an organizational policy, w. These templates are designed by industry experts who. The following is a library of free information security policy templates that map to the hitrust common security framework, which in turn maps to a multitude of security frameworks (nist,. These policy templates align with cis controls v8 and v8.1, enabling. Using group policy objects (gpo) to add membership to a local group can create a security risk if the target group has excessive permissions or rights. Here are a few of the most important information security policies, and guidelines for tailoring them for your organization. Standards a standard is set of prescribed practices or. Our list includes policy templates. This project provides 36 free cybersecurity policy templates. You can start with a data retention policy template that’s been approved by former auditors or bring your own existing policy into the platform. This project provides 36 free cybersecurity policy templates. Defines the protocols for using both personal and corporate devices to ensure sensitive information is protected. Regularly assessing the information security. The following is a library of free information security policy templates that map to the hitrust common security framework, which in turn maps to a multitude of security frameworks (nist,. Cis. These are free to use and fully customizable to your company's it security practices. Learn how to write an information security policy, and download two templates on cybersecurity and network security perimeter policies to get started. Keep reading for more information and best practices for writing your iso 27001 information security policy, plus get an iso 27001 information security policy. Keep reading for more information and best practices for writing your iso 27001 information security policy, plus get an iso 27001 information security policy template with all. Learn how to create an information security policy template that protects your organization’s data from unauthorized access. You can start with a data retention policy template that’s been approved by former auditors or. The templates can be used as an outline of an organizational policy, w. These templates are designed by industry experts who. Standards a standard is set of prescribed practices or. Defines the protocols for using both personal and corporate devices to ensure sensitive information is protected. Using group policy objects (gpo) to add membership to a local group can create. Implementing a comprehensive information security management system (isms) compliant with iso/iec 27001:2023 standards. The templates can be used as an outline of an organizational policy, w. Defines the protocols for using both personal and corporate devices to ensure sensitive information is protected. Cis assembled a working group of policy experts to develop the information security policy templates. The following is. Download our iso 27001 information security policy template to simplify the process and ensure compliant documentation. These are free to use and fully customizable to your company's it security practices. Using group policy objects (gpo) to add membership to a local group can create a security risk if the target group has excessive permissions or rights. The following is a. Sans has developed a set of information security policy templates. The following is a library of free information security policy templates that map to the hitrust common security framework, which in turn maps to a multitude of security frameworks (nist,. Standards a standard is set of prescribed practices or. Regularly assessing the information security. This project provides 36 free cybersecurity. Learn how to create a secure cloud security policy for protecting data and applications in the cloud, including access controls, encryption, and more. Keep reading for more information and best practices for writing your iso 27001 information security policy, plus get an iso 27001 information security policy template with all. Defines the protocols for using both personal and corporate devices. Learn how to create an information security policy template that protects your organization’s data from unauthorized access. Learn how to write an information security policy, and download two templates on cybersecurity and network security perimeter policies to get started. Using group policy objects (gpo) to add membership to a local group can create a security risk if the target group. These are free to use and fully customizable to your company's it security practices. Implementing a comprehensive information security management system (isms) compliant with iso/iec 27001:2023 standards. Standards a standard is set of prescribed practices or. Regularly assessing the information security. Sans has developed a set of information security policy templates. Sans has developed a set of information security policy templates. Regularly assessing the information security. Download our iso 27001 information security policy template to simplify the process and ensure compliant documentation. Defines the protocols for using both personal and corporate devices to ensure sensitive information is protected. Our list includes policy templates. Learn how to create a secure cloud security policy for protecting data and applications in the cloud, including access controls, encryption, and more. Keep reading for more information and best practices for writing your iso 27001 information security policy, plus get an iso 27001 information security policy template with all. The following is a library of free information security policy templates that map to the hitrust common security framework, which in turn maps to a multitude of security frameworks (nist,. These templates are designed by industry experts who. You can start with a data retention policy template that’s been approved by former auditors or bring your own existing policy into the platform. Learn how to create an information security policy template that protects your organization’s data from unauthorized access. Using group policy objects (gpo) to add membership to a local group can create a security risk if the target group has excessive permissions or rights. These policy templates align with cis controls v8 and v8.1, enabling. Learn how to write an information security policy, and download two templates on cybersecurity and network security perimeter policies to get started. Here are a few of the most important information security policies, and guidelines for tailoring them for your organization. The templates can be used as an outline of an organizational policy, w.42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab
42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab
42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab
Security Policy Template 13 Free Word, PDF Document Downloads
42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab
42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab
42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab
42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab
42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab
FREE 9+ Sample IT Security Policy Templates in MS Word PDF
Cis Assembled A Working Group Of Policy Experts To Develop The Information Security Policy Templates.
This Project Provides 36 Free Cybersecurity Policy Templates.
These Are Free To Use And Fully Customizable To Your Company's It Security Practices.
Implementing A Comprehensive Information Security Management System (Isms) Compliant With Iso/Iec 27001:2023 Standards.
Related Post:
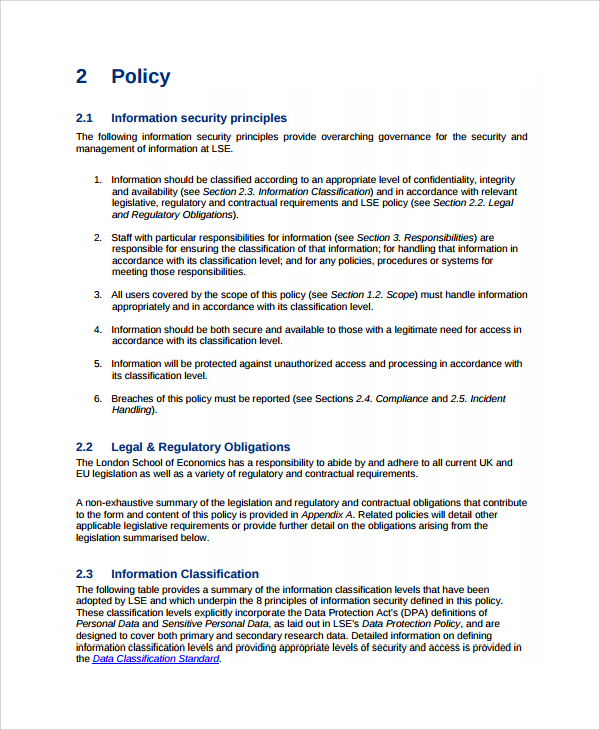
![42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab](https://templatelab.com/wp-content/uploads/2018/05/Security-Policy-36.jpg)
![42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab](https://templatelab.com/wp-content/uploads/2018/05/Security-Policy-12.jpg)
![42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab](https://templatelab.com/wp-content/uploads/2018/05/Security-Policy-10.jpg)
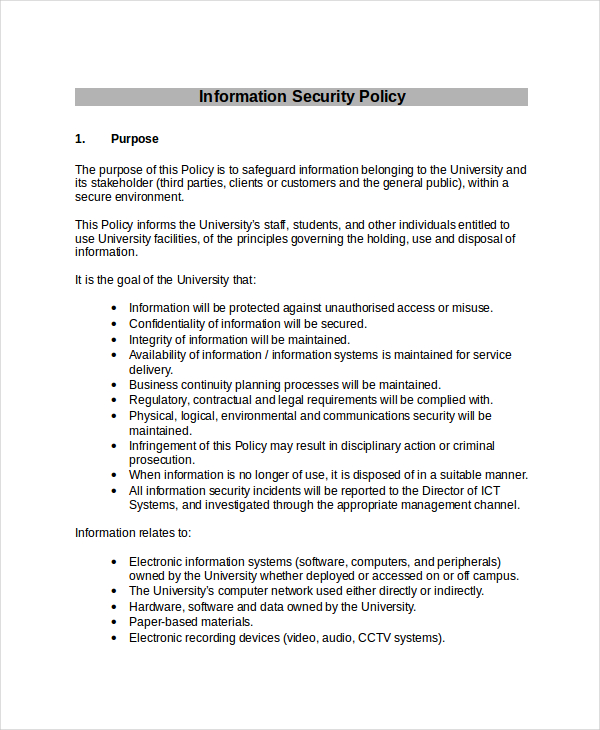
![42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab](https://templatelab.com/wp-content/uploads/2018/05/Security-Policy-24-790x1118.jpg)
![42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab](https://templatelab.com/wp-content/uploads/2018/05/Security-Policy-06.jpg)
![42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab](https://templatelab.com/wp-content/uploads/2018/05/Security-Policy-19.jpg)
![42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab](https://templatelab.com/wp-content/uploads/2018/05/Security-Policy-15.jpg)
![42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab](https://templatelab.com/wp-content/uploads/2018/05/Security-Policy-27.jpg)